IT-security is not only of importance for the sectors water and energy, which are affected by the law for IT-security. The importance is also increasing in other sectors such as manufacturing. Trends like Industry 4.0 or Internet-of-things (IoT) offer the possibility of a data transfer between all participants, provided these use open and normed interfaces. “Open” sounds like “insecure”. Actually, technologies which have been developed web native – just as FlowChief – offer high-level data security, using state of the art standards.
FlowChief is ready for a safe industry 4.0
Software that can’t handle these dynamics will be as useful and common in 10 years as CRT televisions are today. Access via various devices is becoming more and more relevant – and while it takes place directly and securely in modern and open systems, it happens in classical systems via complex client installations or remote dial-in software. These variants may have security gaps and can hardly be controlled.
FlowChief software has been designed to be web-based right from the start and is perfectly tailored to browser and mobile device access through the use of HTML 5 web technology. As other manufacturers took action only as a result of the increased media presence of new attacks on ICS (Industrial Control System), we were already in the midst of the constant development of our security workflows. For example, the security tests are performed by a technical team that works independently of the developers.
IT Security Act – KRITIS
The IT Security Act came into force on 25 July 2015. Operators of critical systems in the fields of energy, information technology and telecommunications, transport and traffic, health, water, nutrition as well as finance and insurance must comply with a minimum standard of IT security and report significant IT security incidents to the Federal Office for Information Security (BSI). The reports received by the BSI are evaluated and then made available as quickly as possible to all operators with the appropriate processing. (Source: www.bmi.bund.de) (Source: www.bmi.bund.de)
Subsequently, on 3 May 2016, the Ordinance on the Determination of Critical Infrastructures (KRITIS) under the BSI Act (BSI-KritisV) became valid. The ordinance defines which facilities fall under the ITSiG and which do not. In concrete terms, around 700 installations in Germany will initially be affected
Further information can be found here:
- www.bsi.de – Federal Office for Information Security
- www.kritis.bund.de – Internet platform for the protection of critical infrastructures
- www.allianz-fuer-cybersicherheit.de – Association of German companies for the exchange of information on the topic – we are members
- Top Ten Bedrohungen für Industrial Control System (ICS)
- BSI Security Kompendium für Hersteller, Systemintegratoren und Anwender – Basic work on IT security measures around ICS
- IT Sicherheitsgesetz
Integrated security with FlowChief
Ensuring the quality
We put a lot of effort into ensuring that our software and code meet the highest security standards. Among other things by the following measures:
- Sensitization and training of our development team
- Profound knowledge in developing secure web technology
- Internal and external penetration tests of our code
- Provision of security patches (also for older systems as part of our product life cycle)
2-factor-authentication
Regulations, such as the German IT-Grundschutz or BDEW Whitepaper, recommend a login procedure based on 2-factor authentication. Independent, state-of-the-art factors should be used. The following procedures are currently available and protect your system against unauthorized login: password entry, authenticator app and SMS transmission comparable to the mobile TAN procedure in online banking.
Password policies & Active Directory support
FlowChief checks the quality of the passwords used. It can be defined how complex the structure must be. On delivery, passwords with two character groups and eight characters are required. The policies prevent the use of the user name in the password. The password policies can not be disabled.
Control your process via browser – no installation, no remote control software
Access to visualization, archive data or alarm management takes place via a web browser. You do not need any remote dial-up software that is difficult to secure.
End-to-end encryption
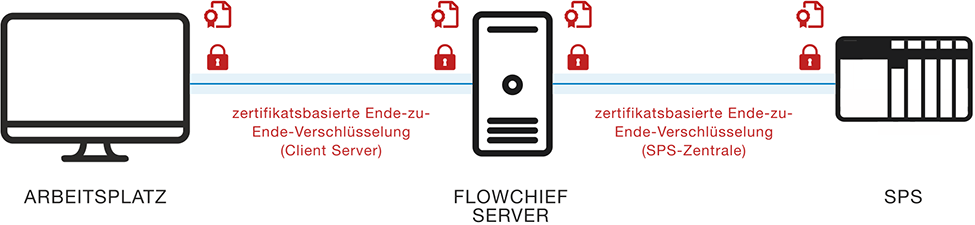 Consistent, X.509 certificate-based TLS encryption of data transmission – both when accessing data between client and server and in communication between all participants using OPC UA.
Consistent, X.509 certificate-based TLS encryption of data transmission – both when accessing data between client and server and in communication between all participants using OPC UA.
Remote control: authentication, encryption and point-to-point connection
FlowChief remote control technology is based on direct, secure and reliable data transmission between RTU (remote terminal unit) and control centre. For the controllers from the manufacturers Wago and Phoenix Contact, there is the option of integrated end-to-end encryption on the basis of X.509 certificates. Controls from other manufacturers can be networked via VPN. Communication is based on a direct point-to-point connection. Root servers are not required for setting up and operating the connections. This means that the remote control technology is independent of provider, service provider or manufacturer.
Holistic security strategy on the basis of deep defence or defence in depth
If one considers the process control system as an asset – i.e. as a unit worth protecting – of a larger infrastructure, the safeguarding of this infrastructure does not end at the application level. The operating system, network level or the security of the plant itself must also be assessed in a holistic concept on the basis of a risk analysis. On the basis of this analysis, measures can be defined to protect each level in line with the threat scenario. Holistic protection of your plant can only be guaranteed through effective cooperation between manufacturers, users, planners and system integrators. We are at the disposal of our customers and partners for this purpose at all times – Please contact us.